Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram

Figure 1 from Applying Dynamic Labels of the Biba Model in Forensic Evidence Analysis | Semantic Scholar
Biba - Biba Integrity Model Presented by Nathan Balon Ishraq Thabet Biba Model 1 Computer Security Computer security is concerned with three aspects | Course Hero
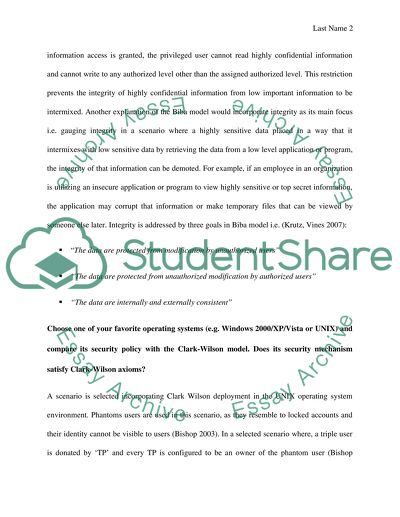
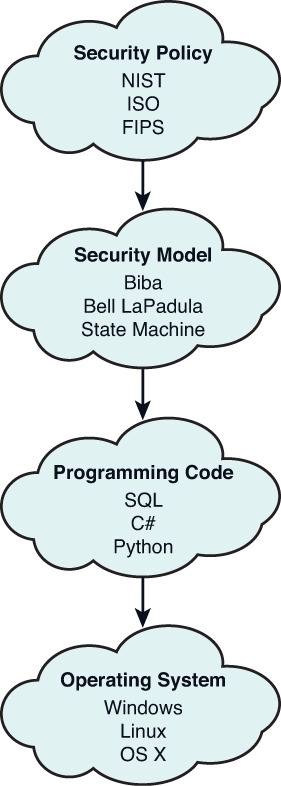
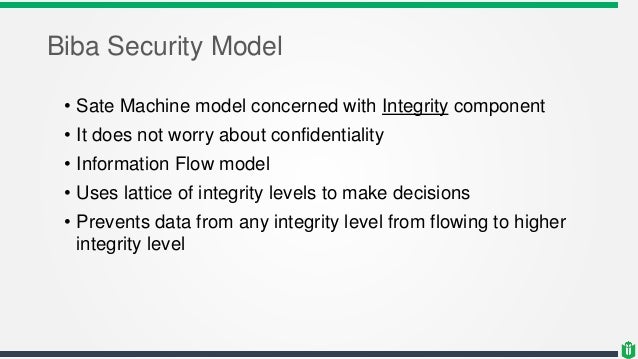
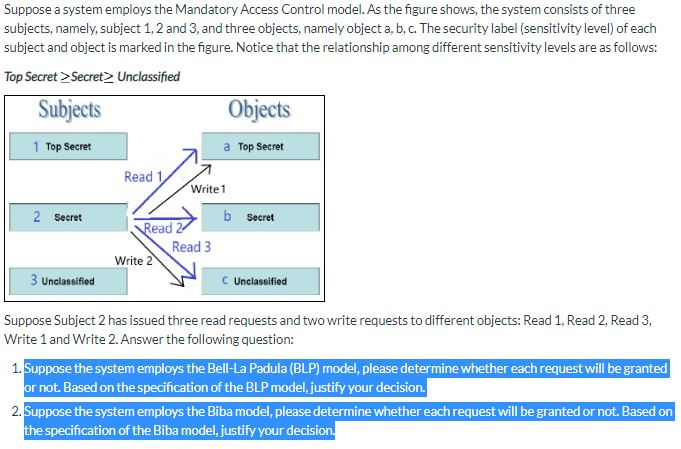
Integrity Models Biba Integrity Model (1977) Biba Model – ”no read down” Biba Model – ”no write up” Biba Model – i